
The Integrated Dependable Architecture for Many Cores (IDAMC) is a many-core processor platform developed at the institute. It is used to research how multi- and many-core architectures can be used in timing- and safety-critical applications.
On the IDAMC, we design and investigate mechanisms that can be used to isolate applications of different criticality, both spatially (e.g. memory addresses) as well as temporally (e.g. accesses over the same memory controller). For such mechanisms, it is important to not only segregate applications of high criticality, but also to retain the throughput of the non-critical applications for efficient mixed-criticality systems.
The IDAMC was originally developed for the RECOMP project, but is now also used in other projects like ASTEROID and ARAMIS.
The following people are currently involved with the IDAMC: Eberle Rambo, Leonardo Ecco, Adam Kostrzewa, Sebastian Tobuschat
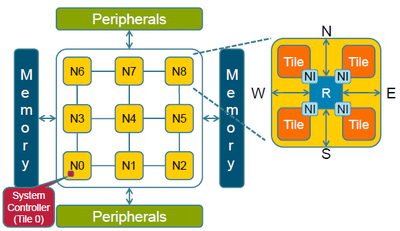
The IDAMC is based on a Network-on-Chip (NoC) composed of nodes (N) connected in e.g. a 2D mesh topology. Each node contains a routers (R) to which multiple tiles can be connected. Each tile itself contains a bus-based sub-system, which may include one or multiple processor cores, on-chip memory, a DDR2 memory controller and other peripherals. Tiles are based on the open-source IP library from Gaisler.
The NoC used in the IDAMC supports quality-of-service (QoS) for multiple traffic classes. This way, we can provide guarantees with respect to bandwidth and latency to safety-critical applications. The QoS is based on the Back Suction mechanism developed in the COMPOSE project. It improves the latency of non-critical applications by exploiting the predictable traffic patterns of safety-critical applications. This improves the throughput of non-safety-critical applications while still providing guarantees to safety-critical applications.
The Network Interface facilitates the access from the local AMBA AHB bus to the NoC. Many safety-features such as system address translation or monitoring are implemented here.
All safety-related features are controlled from a trusted entity, the System Controller. It is the only instance in the system with write access to the configuration space of the safety-critical functions.